On-premises resources – Network Connectivity and Security
To connect to an Azure VPN gateway, you will need a VPN device on your corporate network that supports policy-based or route-based VPN gateways. It also needs to have a public IPv4 network address.
Azure resources
Within Azure, you need to set up the following components:
- VNET: The address space used by the VNET must not overlap with your corporate ranges.
- Gateway subnet: The VPN gateway must be installed in a specific subnet, and it must be called GatewaySubnet. It must have a range of at least /27 (32 addresses).
- Public IP address: An IP address that can be connected to from the public network (internet).
- Local network gateway: This defines the on-premises gateway and configuration.
- VNET gateway: An Azure VPN or ExpressRoute gateway.
The following diagram shows how this might look:
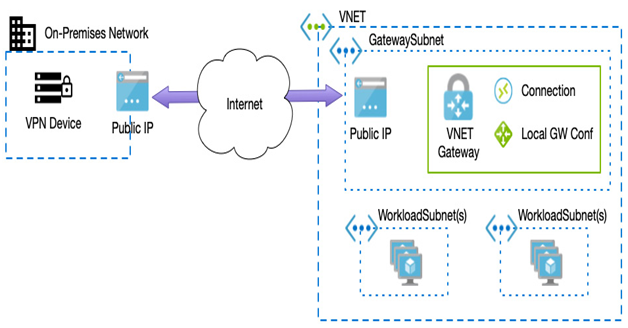
Figure 8.12 – VPN gateway
As we can see from the preceding diagram, a VPN connection is made to a specific subnet and VNET within Azure. In most cases, you would need to connect multiple VNETs to the same connection, which we can perform by peering the connected VNET to your workload VNETs.
This is often called a hub-spoke model; we can see an example hub-spoke model in the following diagram:
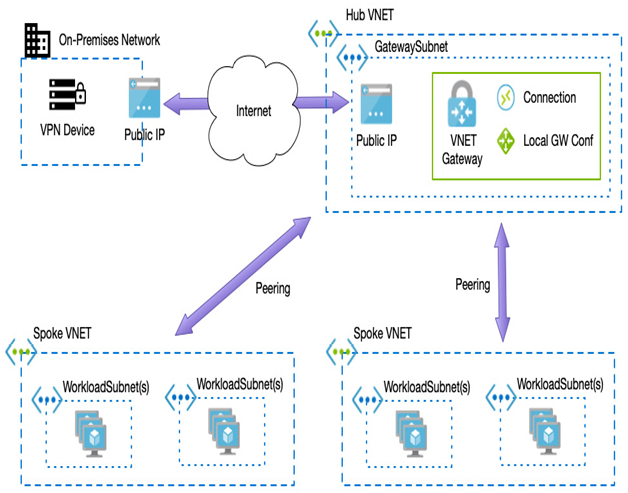
Figure 8.13 – Hub-spoke architecture
Earlier, we stated that connections between VNETs are not transitive, therefore to set up the hub-spoke architecture, we must use a gateway transit – we do this when we create our peering connection between the spoke VNET (which contains our workloads) and the hub VNET (which includes the VNET gateway). On the options when creating a peering request from the spoke to the hub, select the Use the remote virtual network’s gateway option, as we can see in the following example:
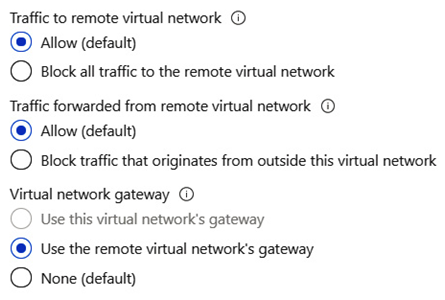
Figure 8.14 – Setting the peering option to use gateway transit
Using a VPN is a simple way to connect securely to Azure. However, you are still using the public network; thus, connectivity and performance cannot be guaranteed. For a more robust and direct connection into Azure, companies can leverage ExpressRoute.
ExpressRoute
ExpressRoute provides a dedicated and utterly private connection into Azure, Office 365, and Dynamics 365. Throughput is significantly increased since connections are more reliable with minimal latency.
Connectivity is via authorized network providers who ensure connections are highly available; this means you get redundancy built-in.
There are three different models to choose from when ordering an ExpressRoute – CloudExchange co-location, point-to-point Ethernet connection, and any-to-any connection:
- CloudExchange co-location is for companies that house their existing data center with an internet service provider.
- Point-to-point connections are dedicated connections between your premises and Azure.
- Any-to-any is for companies that have existing WAN infrastructure. Microsoft can connect to that existing network to provide connectivity from any of your offices.
A key aspect of ExpressRoute is that your connectivity is via private routes; it does not traverse the public internet – except for Content Delivery Network (CDN) components, which by design must leverage the internet to function.
As you leverage more advanced network options, you must have tighter control over traffic flow between VNETs and your on-premises network.
Leave a Reply