Routing – Network Connectivity and Security
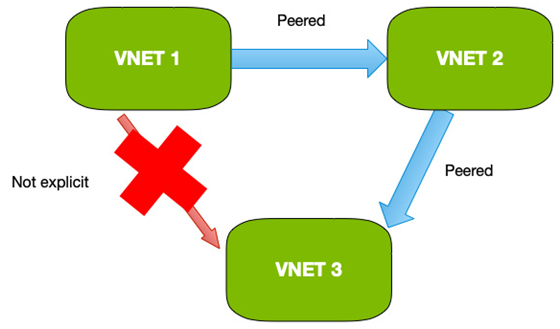
By default, all traffic in Azure follows pre-defined routes that are set up within the VNETs. These routes ensure traffic flows correctly between VNETs and out to the internet as required.
When more advanced routing is required, you can set up your routes to force the traffic through set paths, sometimes known as service chaining.
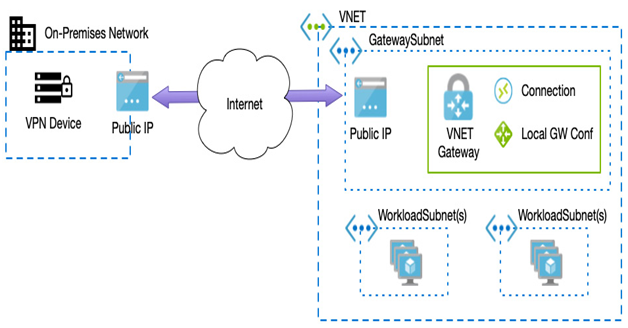
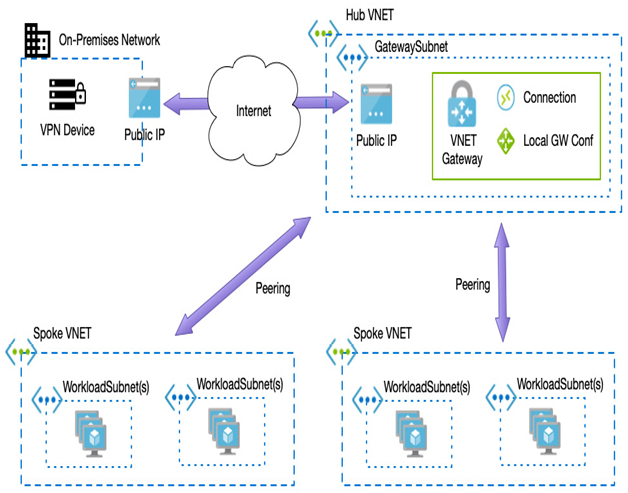
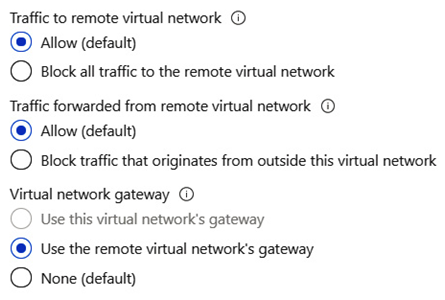
An example is where you need to route your Azure VM traffic back on-premises for your internal ranges. In this instance, you could create a route that sends all traffic destined for your internal ranges to the VPN gateway in your hub VNET.
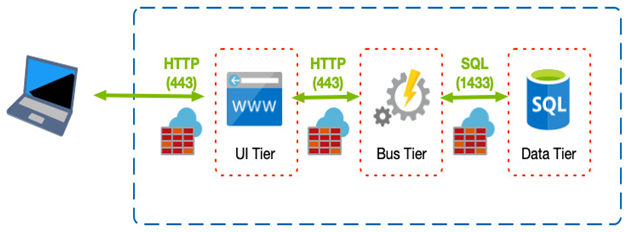
Another example would be when you wish to have all internet traffic traverse a central firewall; in this instance, you would define a route to send all internet traffic to a firewall device you have in a peered VNET.
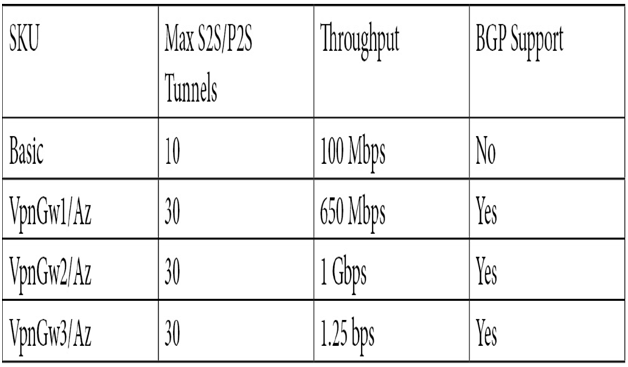
When creating routes, you can create either user-defined routes or Border Gateway Protocol (BGP).
BGP automatically exchanges routing information between two or more networks. In Azure, it can be used to advertise routes from your on-premises network to Azure when using ExpressRoute or a site-to-site VPN.
Alternatively, you can create your custom route; although this is more manual and has a higher administrative overhead, it does provide complete control.
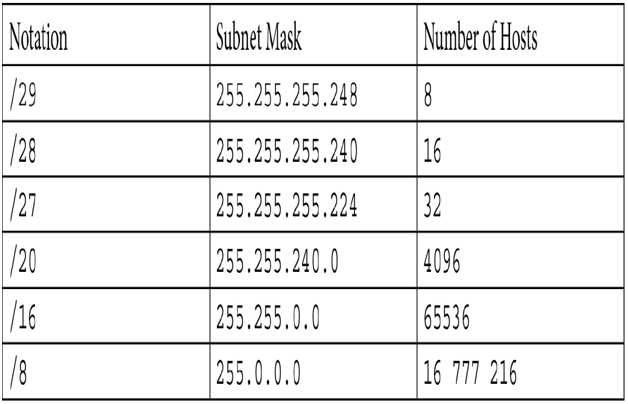
When defining a user-defined route, we set a descriptive name, an address prefix that specifies the address range that we will redirect traffic for, and the next hop. The next hop is where traffic will be routed through and can be any of the following:
- Virtual appliance: Such as a firewall or other routing device
- VNET gateway: Used when directing traffic through a VPN gateway
- VNET: Sends all traffic to a specific VNET
- Internet: Sends traffic to Azure internet routers
- None: Drops all data (that is, blocks all traffic for that range)
For example, if we want to route all traffic through a firewall device with the address of 10.0.0.10, we would create the following custom route:
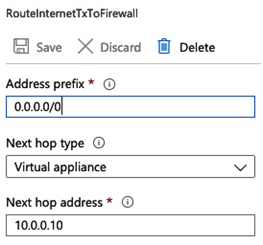
Figure 8.15 – Example user-defined route
We can also add additional routes for other rules; for example, routing traffic through the firewall, we could add another rule to route internal bound traffic to a VPN gateway.
Because we can have a mixture of custom routes, system routes, and BGP routes, Azure uses the following order to decide where to send traffic in the event there is a conflict. That order is as follows:
- User-defined routes
- BGP routes
- System routes
By using a combination, we can precisely control traffic depending on our precise requirements.
Another aspect of routing traffic is when we need to use load balancing components to share traffic between one or more services, and we will discuss this in the next section.