Automating virtual machine management – Designing Compute Solutions-2
For this example, you will need a Windows VM set up in your subscription:
- Navigate to the Azure portal at https://portal.azure.com.
- In the search bar, type and select Virtual Machines and select the virtual machine you wish to apply Update Management to.
- On the left-hand menu, click Guest + host updates under Operations.
- Click the Go to Update Management button.
- Complete the following details:
a) Log Analytics workspace Location: The location of your VM, for example, East US
b) Log Analytics workspace: Create default workspace
c) Automation account subscription: Your subscription
d) Automation account: Create a default account - Click Enable.
The process can take around 15 minutes once completed. Go back to the VM view and again select Guest + host updates under Operations, followed by Go to Update Management.
You will see a view similar to the following screenshot:
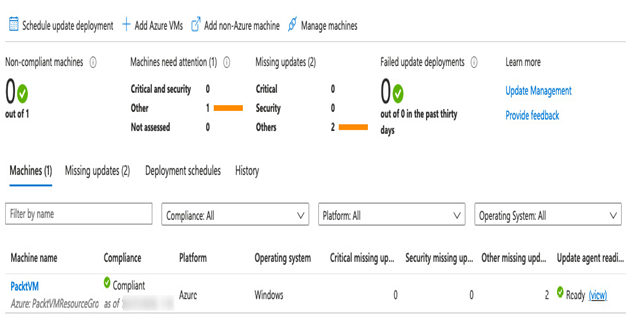
Figure 7.8 – Update Management blade
You can get to the same view but for all the VMs you wish to manage in the portal by searching for Automation Accounts and selecting the automation account that has been created. Then click Update management.
If you want to add more VMs, click the + Add Azure VMs button to see a list of VMs in your subscription and enable the agent on multiple machines simultaneously – as we see in the following screenshot:
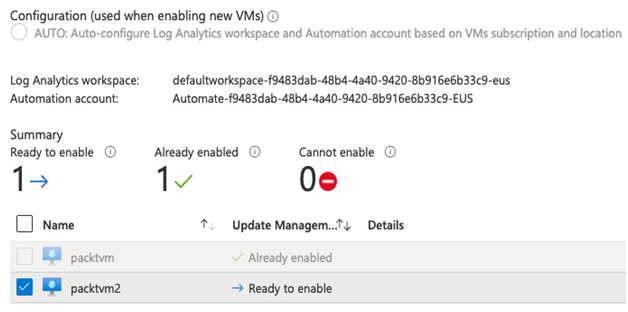
Figure 7.9 – Adding more virtual machines for Update Management
The final step is to schedule the installation of patches:
- Navigate to the Azure portal by opening https://portal.azure.com.
- Type Automation into the search bar and select Automation Accounts.
- Select the automation account.
- Click Update Management.
- Click Schedule deployment and complete the details as follows:
a) Name: Patch Tuesday
b) Operating System: Windows
c) Maintenance Window (minutes): 120
d) RebootReboot options:Reboot if required - Under Groups to update, click Click to Configure.
- Select your subscription and Select All under Resource Groups.
- Click Add, then OK.
- Click Schedule Settings.
- Set the following details:
a) Start date: First Tuesday of the month
b) Recurrence: Recurring
c) Recur Every: 14 days - Click OK.
- Click Create.
Through the Update Management feature, you can control how your virtual machines are patched and when and what updates to include or exclude. You can also set multiple schedules and group servers by resource group, location, or tag.
In the preceding example, we selected all VMs in our subscription, but as you saw, we had the option to choose a machine based on location, subscription, resource group, or tags.
In this way, you can create separate groups for a variety of purposes. For example, we mentioned earlier that a common practice would be to test patches before applying them to production servers. We can accommodate this by grouping non-production servers into a separate subscription, resource group, or simply tagging them. You can then create one patch group for your test machines, followed by another for production machines a week later – after you’ve had time to confirm the patches have not adversely affected workloads.
As part of any solution design that utilizes VMs, accommodation must be included to ensure they are always running healthily and securely, and Update Management is a critical part of this. As we have seen, Azure makes the task of managing OS updates easy and straightforward to set up.
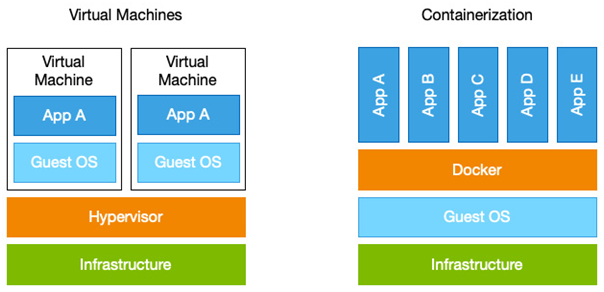
Next, we will investigate another form of compute that is becoming increasingly popular – containerization and Kubernetes.