Azure Functions – Designing Compute Solutions
Azure Functions falls into the Functions as a Service (FaaS) or serverless category. This means that you can run Azure Functions using a consumption plan whereby you only pay for the service as it is being executed. In comparison, Azure App Service runs on a service plan in which you define the CPU and RAM.
With Azure Functions, you don’t need to define CPU and RAM as the Azure platform automatically allocates whatever resources are required to complete the operation. Because of this, functions have a default timeout of 5 minutes with a maximum of 10 minutes – in other words, if you have a function that would run for longer than 10 minutes, you may need to consider an alternative approach.
Tip
Azure Functions can be run as an App Service plan the same as App Service. This can be useful if you have functions that will run for longer than 10 minutes, if you have spare capacity in an existing service plan, or if you require support for VNet integration. Using an App Service plan means you pay for the service in the same way as App Service, that is, you pay for the provisioned CPU and RAM whether you are using it or not.
Functions are event-driven; this means they will execute your code in response to a trigger being activated. The following triggers are available:
- HTTPTrigger: The function is executed in response to a service calling an API endpoint over HTTP/HTTPS.
- TimerTrigger: Executes on a schedule.
- GitHub webhook: Responds to events that occur in your GitHub repositories.
- CosmosDBTrigger: Processes Azure Cosmos DB documents when added or updated in collections in a NoSQL database.
- BlobTrigger: Processes Azure Storage blobs when they are added to containers.
- QueueTrigger: Responds to messages as they arrive in an Azure Storage queue.
- EventHubTrigger: Responds to events delivered to an Azure Event Hub.
- ServiceBusQueueTrigger: Connects your code to other Azure services or on-premises services by listening to message queues.
- ServiceBusTopicTrigger: Connects your code to other Azure services or on-premises services by subscribing to topics.
Once triggered, an Azure function can then run code and interact with other Azure services for reading and writing data, including the following:
- Azure Cosmos DB
- Azure Event Hubs
- Azure Event Grid
- Azure Notification Hubs
- Azure Service Bus (queues and topics)
- Azure Storage (blob, queues, and tables)
- On-premises (using Service Bus)
By combining different triggers and outputs, you can easily create a range of possible functions, as we see in the following diagram:
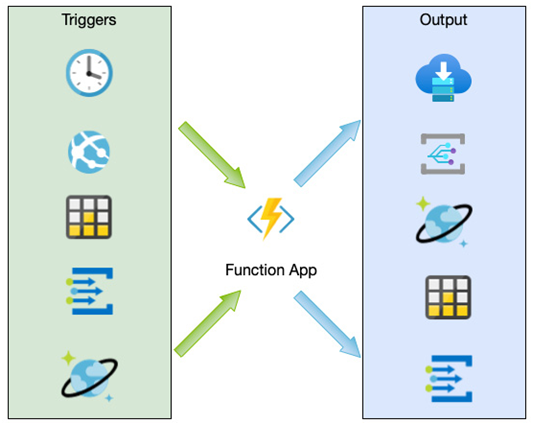
Figure 7.6 – Combining triggers and outputs with a Functions app
Azure Functions is therefore well suited to event-based microservice applications that are short-run and are not continuously activated. As with App Service, Functions supports a range of languages, including C#, F#, JavaScript, Python, and PowerShell Core.